E-Commerce (Elective-II)
NOTE: for any queries please contact us
1. https://www.facebook.com/aakash416/
2. https://www.facebook.com/Aakashraj415
3. mail us aakashraj416@gmail.com
1. https://www.facebook.com/aakash416/
2. https://www.facebook.com/Aakashraj415
3. mail us aakashraj416@gmail.com
Introduction to Electronics Commerce:
Defining Electronics Commerce:
E-commerce (electronic commerce or EC) is the buying and selling of goods and services, or the transmitting of funds or data, over an electronic network, primarily the internet. These business transactions occur either as business-to-business, business-to-consumer, consumer-to-consumer or consumer-to-business. The terms e-commerce and e-business are often used interchangeably. The term e-tail is also sometimes used in reference to transactional processes for online shopping.
History of e-commerce
The beginnings of e-commerce can be traced to the 1960s, when businesses started using Electronic Data Interchange (EDI) to share business documents with other companies. In 1979, the American National Standards Institute developed ASC X12 as a universal standard for businesses to share documents through electronic networks. After the number of individual users sharing electronic documents with each other grew in the 1980s, in the 1990s the rise of eBay and Amazon revolutionised the e-commerce industry. Consumers can now purchase endless amounts of items online, both from typical brick and mortar stores with e-commerce capabilities and one another.
E-commerce applications
E-commerce is conducted using a variety of applications, such as email, online catalogs and shopping carts, EDI, File Transfer Protocol, and web services. This includes business-to-business activities and outreach such as using email for unsolicited ads (usually viewed as spam) to consumers and other business prospects, as well as to send out e-newsletters to subscribers. More companies now try to entice consumers directly online, using tools such as digital coupons, social media marketing and targeted advertisements.
Forces fuelling Electronics Commerce
What forces are fueling e-commerce?
Economic forces: One of the most evident benefits of e-commerce is economic efficiency resulting from the reduction in communications costs, low-cost technological infrastructure, speedier and more economic electronic transactions with suppliers, lower global information sharing and advertising costs, and cheaper customer service alternatives.
Market forces: Corporations are encouraged to use e-commerce in marketing and promotion to capture international markets, both big and small. The Internet is likewise used as a medium for enhanced customer service and support. It is a lot easier for companies to provide their target consumers with more detailed product and service information using the Internet.
Technology forces: The development of ICT is a key factor in the growth of e-commerce. For instance, technological advances in digitising content, compression and the promotion of open systems technology have paved the way for the convergence of communication services into one single platform.
Electronics Commerce Industry Frame work
The basic framework of e-commerce enables doing business online. The framework consists of a comprehensive structure beginning with the based technology layer to the general service layer. E-commerce has, to a certain extent, changed markets structure. Traditionally, market ties were created through the exchange of goods, services, and money. E-commerce has brought in an essential element: information. Market ties are now based on information services, information goods and electronic money. Although the nature of exchanging products remains unchanged, the channel and the format of doing business have changed. To better understand the basic framework of e-commerce, the following paragraphs explain the features of the major layers in the environment of e-commerce.
Basic Framework
1. The First layer: Network Infrastructure
Also known as the “Information Superhighway”, network infrastructure is the foundation layer of hardware infrastructure. It is a mixture of many forms of information transport systems, which include telecom, cable TV, wireless and the Internet. These systems, in particular the Internet, provide various types of telecommunication channels for transmission of contents used in e-commerce.
2. The Second Layer: Multimedia Content and Network Publishing
While the Information Superhighway is the transportation basis that allows content such as text, sounds and images to be transmitted, the second layer provides an architecture that enables the content to be developed in a programming language know as Hyper Text Markup Language (HTML) for publishing on the World Wide Web (WWW). Another programming language in use is Java, which enables multimedia content to be transmitted to end users’ personal computers via various networks such as cable, wireless, fiber optics and satellites.
3. The Third layer: Messaging and Information Dissemination
Messaging transmission is usually done by the following technologies:
(a)Communicating non-formatted data: by using facsimile, electronic mail, which mainly directs to individuals.
(b)Communicating formatted data: by using Electronic Data Interchange (EDI) without human intervention. It is mainly used for business documents such as purchase orders, invoices and packing lists. Messaging transmission technology has encouraged business process automation.
(c) Hyper Text Transfer Protocol (HTTP): HTTP is an information dissemination tool generally used on the Internet. It uses a common display format to publish non-formatted multimedia messages in various environments.
(d)Uniform Resource Locator (URL): URL is at present used by many web surfers to search for information.
4. The Fourth layer: Security Protection in Business Services
This layer is regarded as the essential facilities for doing business because it is required by both business corporations and individuals in business transactions. The facilities include standardized product catalogues, price lists, electronic payment methods, secured transmission of business information, and the authentication of identity of both trading parties. The ultimate goal of e-commerce is that the seller gets the payment and the buyer obtains the product. To ensure transaction security, e-commerce needs to ensure content reliability, integrity, non-repudiation, and to provide the relevant evidence in case of disputes. Therefore, payment security on the web is crucial to ensure smooth completion of a transaction. The prevailing method of security measure is by electronic certification which provides ‘end-to-end’ security protection.
5. The Fifth layer: Practical Application of E-commerce
E-commerce is widely employed in supply chain management, electronic marketing, electronic advertising, online shopping, online entertainment, pay-information service and network banking.
The Last Word
The application of e-commerce has promoted business globalization. Consumers can easily obtain products from other countries via the Internet. This has given rise to issues such as custom clearance and payment of duties. Different countries have different systems and conditions, which may contradict with the cross-border nature of e-commerce. Therefore, international collaboration to develop associated policies and regulations is vital. Crippling laws and regulations will hamper the development of e-commerce.
Types of Electronics Commerce
Generally speaking, when we think of e-commerce, we think of an online commercial transaction between a supplier and a client. However, and although this idea is right, we can be more specific and actually divide e-commerce into six major types, all with different characteristics.
There are 6 basic types of e-commerce:
1. Business-to-Business (B2B)
2. Business-to-Consumer (B2C)
3. Consumer-to-Consumer (C2C)
4. Consumer-to-Business (C2B).
5. Business-to-Administration (B2A)
6. Consumer-to-Administration (C2A)
1. Business-to-Business (B2B)
Business-to-Business (B2B) e-commerce encompasses all electronic transactions of goods or services conducted between companies. Producers and traditional commerce wholesalers typically operate with this type of electronic commerce.
2. Business-to-Consumer (B2C)
The Business-to-Consumer type of e-commerce is distinguished by the establishment of electronic business relationships between businesses and final consumers. It corresponds to the retail section of e-commerce, where traditional retail trade normally operates.
These types of relationships can be easier and more dynamic, but also more sporadic or discontinued. This type of commerce has developed greatly, due to the advent of the web, and there are already many virtual stores and malls on the Internet, which sell all kinds of consumer goods, such as computers, software, books, shoes, cars, food, financial products, digital publications, etc.
3. Consumer-to-Consumer (C2C)
Consumer-to-Consumer (C2C) type e-commerce encompasses all electronic transactions of goods or services conducted between consumers. Generally, these transactions are conducted through a third party, which provides the online platform where the transactions are actually carried out.
4. Consumer-to-Business (C2B)
In C2B there is a complete reversal of the traditional sense of exchanging goods. This type of e-commerce is very common in crowdsourcing based projects. A large number of individuals make their services or products available for purchase for companies seeking precisely these types of services or products.
Examples of such practices are the sites where designers present several proposals for a company logo and where only one of them is selected and effectively purchased. Another platform that is very common in this type of commerce are the markets that sell royalty-free photographs, images, media and design elements, such as iStockphoto.
5. Business-to-Administration (B2A)
This part of e-commerce encompasses all transactions conducted online between companies and public administration. This is an area that involves a large amount and a variety of services, particularly in areas such as fiscal, social security, employment, legal documents and registers, etc. These types of services have increased considerably in recent years with investments made in e-government.
6. Consumer-to-Administration (C2A)
The Consumer-to-Administration model encompasses all electronic transactions conducted between individuals and public administration.
E-Commerce Infrastructure:
Need for Intelligent Website
Here are 10 elements we believe make up an intelligent website.
1. Attracts the Right Audience
2. Data-Driven Design
3. Creates Visibility & Grows Awareness
4. Outsmarts its Competitors
5. Reduces Costs
6. Educates & Inspires Action
7. Increases Leads for More Sales
8. Possesses a Long-term Roadmap
9. Retains Customer Loyalty
10. Helps Companies Become Digitally Empowered
2. Data-Driven Design
3. Creates Visibility & Grows Awareness
4. Outsmarts its Competitors
5. Reduces Costs
6. Educates & Inspires Action
7. Increases Leads for More Sales
8. Possesses a Long-term Roadmap
9. Retains Customer Loyalty
10. Helps Companies Become Digitally Empowered
Web and Database Integration
What is Database Integration? How to Use it in eCommerce?
When you decide it’s time to go beyond a static informational type of web site to something a little more “interactive” for your customers, then your website will probably need to be connected to a database. Database integration or data integration refers to combining a database with your web site so that web visitors can add, remove and update information in your database using a web browser.
Most database integrated sites also allow users to search the database too. Database integrated sites are typically referred to as ‘web applications‘ as they are a cross between a simple ‘static’ HTML site and a full blown software program. And it can be used in many websites which has big database, especially eCommerce websites.
Several ways to carry out dynamic real-time queries from the web:
- Using traditional HTML forms, information is passed to a CGI script that formats the query and submits it to the DBMS. Results are returned to a script which then formats the output in HTML.
- One needs: An HTTP (web) server, some language (e.g., Perl) that supports CGI, middleware to connect to the database, the DBMS.
- Many DBMS now have the web server built in (or closely tied) to the database. e.g., Oracle Web Applications Server. Stored procedures in the DBMS are used to accept input from HTML forms, perform the appropriate query and then format the results in HTML.As an example, consider Oracle 11g and Oracle 12c, where the web server is built into the database.
- Using “Software as a Service” (SaaS). A web service that accepts requests from your web or mobile application. The Web Service then handles querying and manipulating the data on the back-end database.
Web Software development tools
Of the thousands of open source tools, weve tried to list the best among them. Its not been easy to arrive at this list, especially because different people have different, personal favourites.
Node.js
Node.js is a JavaScript runtime built on Google Chromes V8 JavaScript engine. Its an open source cross-platform runtime environment for developing server-side Web applications. Node.js uses an event-driven, non-blocking I/O model, which makes it faster and more efficient. Ryan Dahl is the original author of Node.js. Its initial release was on May 27, 2009.
AngularJS
AngularJS is a JavaScript framework for dynamic Web apps. Its preferable for one-page Web applications. AngularJS supports filters and data-binding with HTML attributes. It has support for forms, form validation and DOM handling. It was originally created by Google and open sourced under the MIT licences. Developed by Brat Tech LLC, Google and the community, its initial release was in 2009.
Bootstrap
Bootstrap is a free, open source tool well known for fast development of responsive designs. It has a set of its own classes and grids, buttons, forms, navigation, containers, media queries and JavaScript extensions. Bootstrap is the most-starred project on GitHub, with over 91,000 stars and more than 38,000 forks.
XAMPP
XAMPP is an open source, cross-platform tool, which is a favourite among Web developers. The full form of XAMPP is X-Cross platform, Apache, MariaDB, PHP and Perl. Earlier, it used MySQL instead of MariaDB. XAMPP is a complete package of these libraries, so developers dont need to worry about installing and configuring PHP, MariaDB and Apache. Its the simplest way to set up a local Web server.
Brackets
Brackets is a popular open source code editor for HTML, CSS and JavaScript. It is developed by Adobe and written in HTML, CSS and JavaScript itself. Brackets makes development faster, as it supports a live preview of the browser in your editor itself. It was initially released on November 4, 2014.
Sublime Text
Let’s start with the basics: a first-rate code editor – one that features a well-designed, super efficient, and ultra speedy user interface. There are several that do this well, but arguably the best (and most popular) is Sublime Text.
Artfully run by a one-man development team, the secret to Sublime’s success lies in the program’s vast array of keyboard shortcuts - such as the ability to perform simultaneous editing (making the same interactive changes to multiple selected areas) as well as quick navigation to files, symbols, and lines. And when you’re spending 8+ hours with your editor each day, those precious few seconds saved for each process really do add up…
Artfully run by a one-man development team, the secret to Sublime’s success lies in the program’s vast array of keyboard shortcuts - such as the ability to perform simultaneous editing (making the same interactive changes to multiple selected areas) as well as quick navigation to files, symbols, and lines. And when you’re spending 8+ hours with your editor each day, those precious few seconds saved for each process really do add up…
Multimedia Web extensions
VRML (Virtual Reality Modelling Language)
VRML (Virtual Reality Modelling Language) is a language for describing three-dimensional ( 3-D ) image sequences and possible user interactions to go with them. Using VRML, you can build a sequence of visual images into Web settings with which a user can interact by viewing, moving, rotating, and otherwise interacting with an apparently 3-D scene. For example, you can view a room and use controls to move the room as you would experience it if you were walking through it in real space.
To view a VRML file, you need a VRML viewer or browser, which can be a plug-in for a Web browser you already have. Among viewers you can download for the Windows platforms are blaxxun's CC Pro, Platinum's Cosmo Player, WebFX, WorldView, and Fountain. Whirlwind and Voyager are two viewers for the Mac.
RealAudio
RealAudio is a continuous or streaming sound technology from Progressive Networks' RealAudio. A RealAudio player or client program may come included with a Web browser or can be downloaded from the RealAudio or other Web sites. To deliver RealAudio sound from your own Web site, you (or your space provider) need to have a RealAudio server.
Internet
While downloading files and viewing websites, you’ll meet up with many file formats. Most are common, and encountered frequently, others are more obscure and require specialist programs to open or use. Here, we have a list of the file types, along with the applications you’ll need to get them going on your computer.
Web based Technology
A web-based application is any program that is accessed over a network connection using HTTP, rather than existing within a device’s memory. Web-based applications often run inside a web browser. However, web-based applications also may be client-based, where a small part of the program is downloaded to a user’s desktop, but processing is done over the internet on an external server.
Directories and search engines
Difference Between Search Engine and Directory
More about Search Engines
The search engine is a web application to search and locate the information or resources on the World Wide Web. With the growth of the resources on the www, indexing the contents in an easily accessible manner became more and more difficult. The solution presented for this problem is the web search engine.
More about Web Directory
A web directory is a hierarchical catalogue of the websites published on the internet. Web sites can submit for cataloguing for these directories, and they are listed under relevant fields in the directory. Usually directories are maintained by human editors and a website is listed only if the site meets a certain criterion which guarantees the authenticity and the quality of the website. Examples of popular web directories are Yahoo! Directory and Open Direct Project. Some directories charge a fee to list the website, while some are free for listing. In both cases, the user has access to the directory without any charges.
Search Engine vs Directory
- Search engines are web application that displays a list of relevant resources available using a database created from indexing information gathered by web crawlers
- Web directory displays a list of relevant resources by a database created by a hierarchical catalogue of websites submitted for listing, where websites are reviewed by human editors.
- Search engines collect information about a website automatically for indexing, while Web directories require a submission from the website to be listed in the directory.
- Websites has to comply a certain criterion to be listed in a directory, to assure standard and quality, while a search engine will automatically list irrespective of the quality of the content. Though search engines use special algorithms to filter and provide the most relevant and useful information for users.
- Some directories charge for listing in the directory, while a search engine does not charge from the publishers.
Business-to-Business (B2B)
Business-to-Business (B2B) e-commerce encompasses all electronic transactions of goods or services conducted between companies. Producers and traditional commerce wholesalers typically operate with this type of electronic commerce.
Business-to-Consumer (B2C)
The Business-to-Consumer type of e-commerce is distinguished by the establishment of electronic business relationships between businesses and final consumers. It corresponds to the retail section of e-commerce, where traditional retail trade normally operates.
These types of relationships can be easier and more dynamic, but also more sporadic or discontinued. This type of commerce has developed greatly, due to the advent of the web, and there are already many virtual stores and malls on the Internet, which sell all kinds of consumer goods, such as computers, software, books, shoes, cars, food, financial products, digital publications, etc.
Consumer-to-Consumer (C2C)
Consumer-to-Consumer (C2C) type e-commerce encompasses all electronic transactions of goods or services conducted between consumers. Generally, these transactions are conducted through a third party, which provides the online platform where the transactions are actually carried out.
Consumer-to-Business (C2B)
In C2B there is a complete reversal of the traditional sense of exchanging goods. This type of e-commerce is very common in crowdsourcing based projects. A large number of individuals make their services or products available for purchase for companies seeking precisely these types of services or products.
Examples of such practices are the sites where designers present several proposals for a company logo and where only one of them is selected and effectively purchased. Another platform that is very common in this type of commerce are the markets that sell royalty-free photographs, images, media and design elements, such as iStockphoto.
3. Legal Framework
3.1 General-Shrink-Weap-Contracts
Introduction
Shrink wrap (and click wrap) contracts are commonly used as an attempt to establish rules on the use of standard software which the software company (ie, the owner of exploitation rights) can directly assert in relation to the end user. In Germany, numerous software products are distributed by means of such a licence structure. However, under German law, it is doubtful whether shrink wrap terms can be effectively agreed.
What is a shrink wrap license?
A shrink wrap license is an end user agreement (EULA) that is enclosed with software in plastic-wrapped packaging. Once the end user opens the packaging, the EULA is considered to be in effect.
There are some concerns about the legality of an agreement that the user cannot examine prior to purchase. To address these concerns, some manufacturers use an onscreen version that the user must agree to before installation can proceed.
What are Shrink Wrap Contract?
Shrink wrap contracts are boilerplate or license agreements or other terms and conditions which are packaged with the products. The usage of the product deems the acceptance of the contract by the consumer. The term ‘Shrink Wrap’ describes the shrink wrap plastic wrapping which coats software boxes or the terms and conditions which come with products on delivery.
What are Click Wrap Contracts?
A clickwrap agreement is mostly found as part of the installation process of software packages. It is also called a “click-through” agreement or click-wrap license. It is a take-it-or-leave-it contract which lacks bargaining power. If a customer likes a product and wants to buy it or avail its service he clicks on ‘I accept’ or ‘Ok’ and if he rejects it, then cannot buy that product or avail that service. Click-wrap agreements can be of the following types: 1. Type and Click where the user must type “I accept” or other specified words in an on-screen box and then click a “Submit” or similar button. This displays acceptance of the terms of the contract. A user cannot proceed to download or view the target information without following these steps. 2. Icon Clicking where the user must click on an “OK” or “I agree” button on a dialog box or pop-up window. A user indicates rejection by clicking “Cancel” or closing the window.
3.2 Laws relating to online Contracts
INTRODUCTION
With recent technological advancement, there is an immense change in the standard of living of people. Thus, communication is no more restricted within its geographical limits and information is transferred much widely and quickly than ever before. Electronic commerce has made its way and many problems are removed through the use of e- commerce which flow as a traditional data. Electronic commerce is a means of the transaction of business electronically and is associated with the buying and selling of information, products and services over computerized communication networks. Though, it is a much broader term encompassing not only Electronic Data Interchange but also other forms of communications such as Electronic Mail and Electronic Bulletin Board.
MEANING OF CONTRACT
The Indian Contract Act, 1872 deals with the principles of law of contract, its essential elements, its formation, its performance and the remedies for the breach of contracts. It determines the circumstances in which promises are made by the parties to a contract, general principles of the formation of contract and also prescribes the remedies which are available in the Court of law for the breach of contract against a person who fails to perform his undertaking created under the Contract.
WHAT IS AN ONLINE CONTRACT
With the advance use of internet and electronic commerce, online contracts have assumed importance mainly in terms of reach and multiplicity. Online contract or an electronic contract is an agreement modelled, signed and executed electronically, usually over internet. An Online contract is conceptually very similar and is drafted in the same manner in which a traditional paper-based contract is drafted. In case of an online contract, the seller who intends to sell their products, present their products, prices and terms for buying such products to the prospective buyers. In turn, the buyers who are interested in buying the products either consider or click on the ‘I Agree’ or ‘Click to Agree’ option for indicating the acceptance of the terms presented by the seller or they can sign electronically. Electronic signatures can be done in different ways like typing the name of the signer’s in the specific signature space, copying and pasting the scanned version of the signature or clicking an option meant for that purpose. Once the terms are accepted and the payment is made, the transaction can be completed. The communication is basically made between two computers through servers. The online contract is brought to the scenario to help people in the way of formulating and implementing policies of commercial contracts within business directed over internet. Online Contract is modelled for the sale, purchase and supply of products and services to both consumers and business associates.
TYPES OF ONLINE CONTRACT
Online contracts can be of three types mainly i.e. shrink-wrap agreements, click or web-wrap agreements and browse-wrap agreements. In our everyday life, we usually witness these types of online contracts. Other types of online contracts include employment contract, contractor agreement, consultant agreement, Sale re-sale and distributor agreements, non-disclosure agreements, software development and licensing agreements, source code escrow agreements.
- Shrink-wrap agreements are usually the licensed agreement applicable in case of software products buying. In case of shrink-wrap agreements, with opening of the packaging of the software product, the terms and conditions to access such software product are enforced upon the person who buys it. Shrink-wrap agreements are simply those which are accepted by user at the time of installation of software from a CD-ROM, for example, Nokia pc-suite. Sometimes additional terms can be observed only after loading the product on the computer and then if the buyer does not agree to those additional terms, then he has an option of returning the software product. As soon as the purchaser tears the packaging or the cover for accessing the software product, shrink-wrap agreement gives protection by indemnifying the manufacturer of the product for any copyright or intellectual property rights violation. Though, in India, there is no stable judicial decision or precedent on the validity of shrink-wrap agreements.
- Click- wrap agreements are web based agreements which require the assent or consent of the user by way of clicking “I Agree’ or “I Accept” or “Ok” button on the dialog box. In click –wrap agreements, the user basically have to agree to the terms and conditions for usage of the particular software. Users who disagree to the terms and conditions will not be able to use or buy the product upon cancellation or rejection. A person witnesses web-wrap agreements almost regularly. The terms and conditions for usage are exposed to the users prior to acceptance. For agreement of an online shopping site etc.
- An agreement made intended to be binding on two or more parties by the use of website can be called a browse wrap agreement. In case of browse wrap agreement a regular user of a particular website deemed to accept the terms of use and other policies of the website for continuous use.
3.3 Jurisdiction of Owner Website
Until the Internet's advent, a business operating within one state was subject to suit only in that state. Only a business developing a national or international focus had to assess the risk of becoming subject to suit in other states or countries. Performing that risk assessment was usually simple. Traditionally, whether a particular court can exercise control over a particular defendant depends on their physical locus, described in such terms as residence, domicile or place of business. For example, a corporation can generally be sued in any state where it maintains a place of business.
Personal Jurisdiction Basics
The judicial decisions to date in the United States, regardless of their result, are based upon well-developed and long established personal jurisdiction doctrines. Understanding these doctrines is essential to analyzing the emerging decisional law related to Internet use. Personal jurisdiction is based on the interaction between an affirmative statutory or common-law source law dictating the scope of the court's jurisdiction, and limitations imposed by constitutional due process rights.
Personal Jurisdiction, Multimedia and Broadcasting
In evaluating the ability to obtain personal jurisdiction over a defendant due to operation of a Web site, a parallel can be drawn to print publications. Print publications, like Web sites, come into contact with several jurisdictions, based on conduct that occurs primarily in one location. Print publications are created by conduct concentrated at the location of the author and publisher.
Personal Jurisdiction Based on Internet Contacts
Based on the rules expressed in cases like IDS Life Insurance and Gaingolo, operating a Web site or advertising on the Internet should not, by itself, subject a party to global jurisdiction. But, based on the Keeton and Calder decisions, a person committing a tortious act using the Internet should expect to be subject to jurisdiction in the state at which the tortious act is directed.
International Personal Jurisdiction
Cases examining whether a Web site maintained outside of the United States can allow a United States court to exercise personal jurisdiction over the Web site owner follow the same analysis as the purely domestic cases.
Conclusion
A company putting a Web site on the Internet should remain aware that its Web site may expand the geographic scope of its business. Depending on the nature of the business and the Web site content, the company might now be directing its activities toward customers in other states and countries.
5 Electronics Commerce, banking and Retailing
5.1 Home Banking
Home banking is another feature in banking services. As with increase in technology you get to use many banking facilities sitting at home or any convenient place you like. In simple words home banking means you do not go to bank branch only. However you sit at home and continue with bank processes. In addition there are advantages of home banking also. You can keep reading to know more about this here.
5.1.What do you mean by home banking?
Definition of the term home banking is simple to understand. It is so because as name says it is home banking. So you bank from home only. Even you bank using internet or your telephone. Though internet banking started in 1980s still home internet banking became popular in 1990s.
Sponsored Links:
As a result you do not go to bank for any banking transactions. However you go to only home banking option of your bank to access banking services. Further you get chance to manage accounts from any place in world.
You also use different services. Thus it makes banking experience easy and manageable. Below you check list of home banking services that you use from.
Features of home banking
- Pay bills while you are at home
- Online transactions
- Check account details
- Get notifications or alerts about account activity on your phone through text message
- Or you may receive alerts or notifications regarding your bank account through registered email ID
- Finally you use one simple and secure home banking option
Some more services and advantages of home banking
Apart from above stated home banking features you do not worry about extra charges on use of home banking options. It is so because you use services such as accessing bank accounts funds or other services through computer.
There are some people who call it as internet banking also. While there are other people who call it as electronic banking. As you take help of internet to access account information. There is also net banking option.
You can know more about internet banking here. People also call it as online banking advantages and disadvantages. Hence it is better that you check net banking definition and features of internet banking.
What are the advantages and disadvantages of home banking?
As you know there are many advantages and disadvantages of home banking. But before that you should know what do you mean by home banking system. As this term of home banking or banking from home means that you bank from your home.
Moreover you do not have to go to bank personally. It is so because you get all facilities in home banking system only. Besides there is option for home banking software. On other hand you should have home banking ID.
As home banking ID helps you to use home banking system or the home banking software. In addition idea of best investment options in India will be plus point.
5.2 Banking via the PC using Internet/Intranet
The main companies that are working to develop home banking software are intuit, the marker of Quicken; Microsoft, the maker of Microsoft Money; bank of America and Nations Bank, who acquired Meca's Managing Your Money software from H&R block; and ADP, which acquired Peachtree software.
Intuit is the leading provider of home and small business financial software, supplies, and services for PC users. It pioneered computerized personal. Finance Management with the introduction of the Quicken program in October 1948. Intuit has consistently been in the forefront of new online financial services, launching bill payment services in 1990, Intellicharge credit card services in 1993, and Quicken Quotes, a portfolio price update service, in 1994. In recent years the Company benefited for both the personal computer boom and its giving consumers a diverse product breadth and a software bundle focus, including offerings on personal finance, small business finance, financial planning tax preparation, and bill payment and transactions.
Since its introduction, Quicken has been enhanced and upgraded several times. Quicken allows users to organize, understand, and manage their personal finances. Designed to look and work like a checkbook, Quicken provides users with a method for recording and categorizing their financial transactions. Once entered, the financial information cab be analyzed and displayed using a set of reports and graphs. Quicken also allows users to reconcile their bank accounts and track credit card purchases, investments cash and other assets and liabilities. It enables users to make payments by printing computer checks or by initialing electronic payments via modem. Serveral factors, including good design, affordable pricing and the availability of new features and services, have contributed to quicken's success.
As a complement to its personal financial software products intuit offers value added such as online banking bill payment and credit management that further automate users financial transactions. Online banking is a new feature of quicken 5 for windows, wihich was released in the first quarter of fiscal 1996. Intuit's online banking services, in conjunction with the services of intuit's financial institution partners, allow users to download and automatically categorize savings and loan account activity, brokerage activity, and charges account activity, thereby reducing data entry and providing an easily accessible view of their financial portfolio.
5.3 Banking via online services
Although personal finance software allows people to manage their money, it only represents half of the information management equaltion. No matter which software package is used to manage accounts, information gets managed twice once by the consumer and once by the bank. If the consumer uses personal finance software , then both the consumer and the bank are responsible for maintaining systems unfortunately, these systems do not communicate with one another thus giving new meaning to double entry bookkeeping.
Unfortunately, off-the -shelf personal finance software cannot bridge the communications gap or reduce the duplication of effort described above. But a few thome banking systems that cab help are beginning to take hold. In combination with a PC and modem these home banking services let the bank become an electronic gate way, reducing the monthly paper chase of bills and checks.
Citibank and Prodigy to understand the more contemporary online banking services, we look at citibank and prodigy. Prodigy has been providing home banking to consumers since 1988, and has relationships with more banks than any commercial online service.
To expand the attractiveness of its online banking services, in 1996 citibank began offering prodigy subscribers a free and direct link to its electronic home banking service. Access to Citibank is available to prodigy subscribers at no extra fee throughout the the New York metropolitan area. The agreement represents the first time that citibank has expanded access to its proprietary PC banking service though a commercial onlinge service. To encourage citibank customer to try online baking through Prodigy, free prodigy software will be made available at local Citibank branches. CitiBanking on prodigy offers a full range of banking services . customers can check their account balances, transfer money between accounts, pay bills electronically, review their Citibank credit card account, and buy and sell stock through CitiCorp investment services. Citibank and prodigy allow customer to explore the wide array of services using an interactive, hands on demonstration.
5.4 Banking via Web
Security first network bank with explosive growth in internet use banking via the world wide web will undoubtedly catch on quickly. The goal of this approach to banking is to provide superior customer service and convenience in a secure electronic environment. The competitors in this segment are baks that are setting up web sites, and firms like intuit that cab easily transport their product ot the internet.
How is internet banking different form online banking? This is an important question and the answer is often misunderstood. Banking on the internet is not the same as banking via online services. Internet banking means that:
Consumers do not have to purchase any additional software, store any data on their computer, back up any information, or wait months for new versions and upgrades, since all transactions occurs on a secure server over the internet.
Consumers can conduct banking anywhere as long as they have a computer and a modem whether at home at the office, or in a place outside the united states, banking via online services is restrictive in that the consumer has to install a software package onto her computer. This limits the customer to banking only from that computer making a call to access a separate network working with a separate software company, and banking during limit hours of operation. Consumers can download account information into their own choice progrmas rather than following the dictates of the service provider.
Internet banking allows banks to break out of the hegemony of software developers. If bank customers install personal finance management software on their PCs, these customers become direct customers of software firms, buy controlling the software interface, software firms such as intuit cab control the kinds of transactions end users make and with whom these transactions occur. By maintaining a direct relationship with end users via the web banks cab offer additional services and provide a personal feel to the interface, without seeking the cooperation of a software company.
5.6 Changing Retail industry dynamics.
Important factors affecting the retailing industry dynamics are:
- Overbuilding and excess supply.
- Changes in consumer demographics, with more premium placed on efficient use of time.
- Changes in consumer behavior, with less focus on brand name and more on lowest prices.
- Technology improvements that provide greater convenience and more information than traditional retailing.
Overbuilding and Excess Capacity
Demographic Changes- With online retailing, constraints of time and space disappear.
- It can severely affect companies that have invested in expansion and adding capacity.
- Inadequate productivity, both per worker and per unit of space, is reducing profit margins.
- Overbuilding also resulted in a growing shortage of low-cost, entry level workers for the retail industry.
- Clearly, with crowded domestic markets and competition constantly grinding away at operating profit, new ways of retailing are being exploded by forward thinking companies.
- Shopping patterns are beginning to change with the increase of time-strapped, two-career couples.
- Recent retail data shows a decline in the amount of time Americans are spending in shopping malls. The reasons vary: time constraints, safety concerns, and growing frustration with the lack of courteous service and insufficient product information.
- As technology improves, it may not be long before driving to the store gives way to online shopping with home delivery.
- In contrast, there is a growing segment of the population for whom time constraints are less of a problem.
- Retailers will need to concentrate on value by offering new product mixes that include not only merchandise but also bundles in entertainment and "recreational" shopping with movie theaters, restaurants, bookstores, libraries, and community meeting facilities.
Consumer Behavior
- Consumer behavior is more volatile than ever before, and companies need new ways of responding to consumer needs and satisfying demand.
- Retailers provide consumers with a very large selection of producers priced with deep discounts like power centers, discount malls, discount stores, and catalog shopping.
- Consumers are no longer as influenced by brand names as they used to be.
- Retailers that are focused on providing value-the best price, service, and selection will be successful.
5.7 Technology improvements in Electronics retailing
Three dominant forms of electronic retailing channels are: television retailing, CD-ROM retailing, and online service-based retailing, in which we include Web-based retailing.
Television Retailing:The breadth and reach of TV retailing are amazing. Unlike
online audiences, which tend to be predominantly affluent and well educated, the target audience for television retailing is moderate income households and mostly women. The TV retail marketing and programming are divided into segments that are televised live, with a show host who presents the merchandise and conveys information relating to the product, including price, quality, features and benefits. Viewers place orders for products by calling a toll-free telephone number. More recently, infomercials have become a crucial retailing topic. Modern filming techniques and ingenuity make it possible to create high-quality, cost-efficient, and entertaining documentaries that sell.
CD-ROM based Shopping: Relatively inexpensive to produce and distribute, CD-ROMs represent a cost-effective alternative to traditional print catalogs. The crucial business ideas behind catalogs is threefold: build name and brand recognition for the stores and manufacturers; help determine store expansion plans by using the catalog as a prospecting tool; and develop inventory control mechanisms that reduce excess capacity by creating alternative distribution avenues. However there are several disadvantages to the medium, the most obvious being that not everyone has a CD-ROM drive. Once a disk is created, it cannot be updated.
Online-based Shopping: Online retailers can be divided into four major groups:
- Retailers that operate off-line stores, getting their feet wet with online storefronts.
- Retailers such as catalogers who are concerned with new Web-based methods of catalog retailing.
- "New age" retailers that do not currently operate retail business, but they understand how this new medium can revolutionize shopping.
- Manufacturers exploring the potential to go "direct to consumers".
- Retailers are increasingly looking toward the Web as a retail outlet because of its reach, constant innovation, and low cost. Online shopping can be delivered 24 hours a day and 7 days a week. The intriguing aspect of online retailing is the emergence of companies that only exist online.
5.8 Mercantile models from consumer’s perspective
- Each consumer has a distinct way of doing business but still some generalization can be made about the way consumers do shopping.
- Mercantile models create consistency and increase consumer convenience by eliminating the need to figure out a new business process for every single vendor.
- Mercantile model can be developed from two perspectives: consumer and retailer.
- From the consumer side, it specifies the sequence of activities a shopper takes in purchasing a product or service.
- From the retailer side, it defines the order management cycle, which specifies the activities within an organization that must take place in fulfilling the customer's order.
Distinct phases of a Consumer Mercantile Model
They can be grouped into three phases:
- The prepurchase preparation phase includes search and discovery for a set of products in the larger information space capable of meeting customer requirements and product selection from the smaller set of products based on attribute comparison.
- The purchase consummation phase specifies the flow of information and documents associated with purchasing and negotiation with merchants for suitable term and electronic payment mechanisms that integrate payment into the purchasing process.
- The postpurchase interaction phase includes the customer service and support to address customer complaints, product returns, and product defects.
Types of Consumers: Consumers can be categorized into three types:
- Impulsive Buyers, who purchase products quickly
- Patient buyers, who purchase products after making some comparisons
- Analytical buyers, who do substantial research before buying.
Next topic is coming soon
8. Advanced Topics:
8.1 Mobile Commerce
M-commerce (mobile commerce) is the buying and selling of goods and services through wireless handheld devices such as cellular telephone and personal digital assistants (PDAs). Known as next-generation e-commerce, m-commerce enables users to access the Internet without needing to find a place to plug in. The emerging technology behind m-commerce, which is based on the Wireless Application Protocol (WAP), has made far greater strides in Europe, where mobile devices equipped with Web-ready micro-browsers are much more common than in the United States.
In order to exploit the m-commerce market potential, handset manufacturers such as Nokia, Ericsson, Motorola, and Qualcomm are working with carriers such as AT&T Wireless and Sprint to develop WAP-enabled smart phones, the industry's answer to the Swiss Army Knife, and ways to reach them. Using Bluetooth technology, smart phones offer fax, e-mail, and phone capabilities all in one, paving the way for m-commerce to be accepted by an increasingly mobile workforce.
As content delivery over wireless devices becomes faster, more secure, and scalable, there is wide speculation that m-commerce will surpass wireline e-commerce as the method of choice for digital commerce transactions. The industries affected by m-commerce include:
- Financial services, which includes mobile banking (when customers use their handheld devices to access their accounts and pay their bills) as well as brokerage services, in which stock quotes can be displayed and trading conducted from the same handheld device
- Telecommunications, in which service changes, bill payment and account reviews can all be conducted from the same handheld device
- Service/retail, as consumers are given the ability to place and pay for orders on-the-fly
- Information services, which include the delivery of financial news, sports figures and traffic updates to a single mobile device
8.2 Wireless Application Protocol (WAP)
Wireless application protocol (WAP) is a communications protocol that is used for wireless data access through most mobile wireless networks. WAP enhances wireless specification interoperability and facilitates instant connectivity between interactive wireless devices (such as mobile phones) and the Internet.
WAP functions in an open application environment and may be created on any type of OS. Mobile users prefer WAP because of its ability to efficiently deliver electronic information.
The WAP cascading style sheet (CSS) is a mobile rendering of the World Wide Web that allows developers to format screen sizes for mobile device adaptability. Reformatting is not required when using WAP CSS content, which controls page layout compatibility with a variety of mobile device display screens.
The core interface of WAP architecture is the WAP datagram protocol, which manages the transmission layer protocols of Internet models and facilitates operations between mobile wireless networks and platforms, independent of upper layer protocols. The transport layer deals with physical network issues, allowing wireless global operations to readily access wireless gateways. A WAP gateway is a server that facilitates wireless network access.
The WAP Forum, now known as the Open Mobile Alliance (OMA), provides WAP tool testing, specification development and support for all mobile services.
8.3 Generations of Mobile Wireless Technology
Mobile wireless industry has started its technology creation, revolution and evolution since early 1970s. In the past few decades, mobile wireless technologies have experience 4 or 5 generations of technology revolution and evolution, namely from 0G to 4G. The cellular concept was introduced inthe 1G technology which made the large scale mobile wireless communication possible. Digital communication has replaced the analogy technology in the 2G which significantly improved the wireless communication quality. Data communication, in addition to the voice communication, has been the main focus in the 3G technologies and a converged network for both voice and data communication is emerging. With continued R&D, there are many killer application opportunities for the 4G as well as technological challenges.
- 1G – A term never widely used until 2G was available. This was the first generation of cell phone technology. Simple phone calls were all it was able to do.
- 2G – The second generation of cell phone transmission. A few more features were added to the menu such as simple text messaging.
- 3G – This generation set the standards for most of the wireless technology we have come to know and love. Web browsing, email, video downloading, picture sharing and other Smartphone technology were introduced in the third generation. 3G should be capable of handling around 2 Megabits per second.
- 4G – The speed and standards of this technology of wireless needs to be at least 100 Megabits per second and up to 1 Gigabit per second to pass as 4G. It also needs to share the network resources to support more simultaneous connections on the cell. As it develops, 4G could surpass the speed of the average wireless broadband home Internet connection. Few devices were capable of the full throttle when the technology was first released. Coverage of true 4G was limited to large metropolitan areas. Outside of the covered areas, 4G phones regressed to the 3G standards. When 4G first became available, it was simply a little faster than 3G. 4G is not the same as 4G LTE which is very close to meeting the criteria of the standards.
- 4G LTE – Long Term Evolution – LTE sounds better. This buzzword is a version of 4G that is the latest advertised technology and is getting very close to the speeds needed as the standards are set. When you start hearing about LTE Advanced, then we will be talking about true fourth generation wireless technologies because they are the only two formats realized by the International Telecommunications Union as True 4G at this time. But forget about that because 5G is coming soon to a phone near you. Then there is XLTE which is a bandwidth charger with a minimum of double the bandwidth of 4G LTE and is available anywhere the AWS spectrum is initiated.
- 5G – There are rumors of 5G being tested although the specifications of 5G have not been formally clarified. We can expect that new technology to be rolled out around 2020 but in this fast-paced world it will probably be much sooner than that. Seems like a long ways away but time flies and so will 5G at speeds of 1-10Gbps.
8.4 Components of Mobile Commerce
1. Wireless Communication Component:
Wireless communication component are that medium in which the signals are not guided through a solid medium. In wireless system air is the media through which electromagnetic energy can flow easily and communication involves in several directions.
The wireless methods include radio based and satellite based, light based wireless system.
A- Radio waves, satellite and paging system uses radio frequency signals the range of frequency lies between 100 Khz to 20 Ghz.
2. Sattellite based Wireless System-
Sattellite microwave system transmit signals between directional parabolic antennas. A Communication satellite is a microwave relay station placed 36000 K above the equator. Satellite placed in geo synchronous orbit, it appears to be stationary relative to earth and always stay over the same point with respect to earth. Satellite frequency range lies between 4-6 Ghz and 11-14 Ghz.
3. Light Based Communication System:
Light based system usage light to sending pulses that emmitted in a LED to a photo sensor that decode the signals.
Light based communication system have two categories-
- Low speed device
- High Speed device
8.5 Networking Standards for Mobiles
Networking Standards for Mobiles are three types:
1 GSM
GSM was developed by the European Telecommunications Standards Institute to replace the analog networks we knew and didn’t love. The first GSM networks started popping up in the early-to-mid 1990s. In the decade and a half since, it has become the de facto standard when it comes to worldwide communications, with a couple notable exceptions.
While it was not part of the initial specification, modern GSM devices use a Security Identity Module. This little chip card contains the International Mobile Subscriber Identity (IMSA) Number, carrier information, and your contact information. Assuming the phone is not carrier locked, the SIM card slot allows you to easily migrate your phone between carriers. Galaxy Note 8 Release date will be on 2017 and it will be released with LTE.
2 CDMA
The other well-travelled cellular technology is CDMA. CDMA was developed by Qualcomm. The CDMA brand name encompasses two different standards: IS-95 aka CDMA One, a 2G digital service, and its modern 3G successor CDMA-2000. As far as i can tell, just about every CDMA carrier is using the later standard. While there is an analog to the SIM card called RUIM, they have not been widely used with carriers in the Americas. In those markets, that data is stored on the phone itself which has made moving your phone between carriers effectively impossible.
“3G” Data is provided by Evolution Data Optimized (EV-DO). EV-DO is technically on its 4th version, Rev. C, but the majority of carriers are using Rev. A. From a technical standpoint, EV-DO has two historical disadvantages compared to UTMS/HSPA data on the GSM path. First off, CDMA phones have not been able to conduct simultaneous voice and data sessions. In other words, if you’re talking, you can’t use cellular data. This has been fixed very recently with a variant called SV-DO.The other is not as easily fixed. EV-DO is reasonably competitive with early UMTS speeds, but hasn’t evolved much beyond that. Because of the less than ideal speeds, CDMA carriers started to look for other options. Sprint has offered Clearwire’s WiMAX network as a “4G” solution. Verizon, on the other hand, started an early transition to LTE.
3 LTE
While Long Term Evolution (LTE) is part of the GSM path, it will be the only cellular technology going forward. It has been introduced in data form by most carriers and in widespread use by Verizon. Voice over LTE (VoLTE) will eventually handle your voice calls as well. That being said, LTE is not fully baked by any means and requires some technology advancement to be fully realized. LTE also comes in two different flavors: Frequency-Division Duplexing (FDD) used in the west, and Time-Division Duplexing (TDD).
If you’ve used it on a carrier with sufficient bandwidth, LTE is fast. Unless you’re in Kansas City with Google Fiber, LTE will probably be faster than your home broadband connection. That’s both a blessing and a curse. Since data allotments have not changed with the faster speeds and larger file sizes, you can find yourself with an excessively large phone bill if you’re not not careful. An upgraded version, LTE advanced, will make it even faster.
8.6 Electronic Data Interchange
What is EDI and how can it help your business?
By moving from a paper-based exchange of business document to one that is electronic, businesses enjoy major benefits such as reduced cost, increased processing speed, reduced errors and improved relationships with business partners.
Each term in the definition is significant:
- Computer-to-computer– EDI replaces postal mail, fax and email. While email is also an electronic approach, the documents exchanged via email must still be handled by people rather than computers. Having people involved slows down the processing of the documents and also introduces errors. Instead, EDI documents can flow straight through to the appropriate application on the receiver’s computer (e.g., the Order Management System) and processing can begin immediately. A typical manual process looks like this, with lots of paper and people involvement:
- Business documents – These are any of the documents that are typically exchanged between businesses. The most common documents exchanged via EDI are purchase orders, invoices and advance ship notices. But there are many, many others such as bill of lading, customs documents, inventory documents, shipping status documents and payment documents.
- Standard format– Because EDI documents must be processed by computers rather than humans, a standard format must be used so that the computer will be able to read and understand the documents. A standard format describes what each piece of information is and in what format (e.g., integer, decimal, mmddyy). Without a standard format, each company would send documents using its company-specific format and, much as an English-speaking person probably doesn’t understand Japanese, the receiver’s computer system doesn’t understand the company-specific format of the sender’s format.
- Business partners – The exchange of EDI documents is typically between two different companies, referred to as business partners or trading partners. For example, Company A may buy goods from Company B. Company A sends orders to Company B. Company A and Company B are business partners.
The Need for EDI
For companies of any size, implementing EDI is necessary for maximum competitiveness and growth. It reduces costs and improves operational performance across your organization. From the start, EDI accelerates data exchange and sharpens accuracy. Your company and your customers benefit from streamlined administration, improved information flow, more accurate accounting, better inventory management, and lower costs. Because electronic transactions are so efficient, customers that use EDI prefer to work with vendors that have EDI systems in place.
From financial, operational, and technical perspectives, the right EDI solution makes irrefutable business sense.
From financial, operational, and technical perspectives, the right EDI solution makes irrefutable business sense.
Key Benefits of EDI:
- Reduces or eliminates manual data-entry errors
- Streamlines transaction processing
- Increases productivity without increasing staff
8.7 E-CRM(Electronic customer relationship management)
Electronic customer relationship management (E-CRM) is the application of Internet-based technologies such as emails, websites, chat rooms, forums and other channels to achieve CRM objectives. It is a well-structured and coordinated process of CRM that automates the processes in marketing, sales and customer service.
An effective E-CRM increases the efficiency of the processes as well as improves the interactions with customers and enables businesses to customize products and services that meet the customers’ individual needs.
Electronic customer relationship management provides an avenue for interactions between a business, its customers and its employees through Web-based technologies. The process combines software, hardware, processes and management’s commitments geared toward supporting enterprise-wide CRM business strategies.
Electronic customer relationship management is motivated by easy Internet access through various platforms and devices such as laptops, mobile devices, desktop PCs and TV sets. It is not software, however, but rather the utilization of Web-based technologies to interact, understand and ensure customer satisfaction.
An effective E-CRM system tracks a customer’s history through multiple channels in real time, creates and maintains an analytical database, and optimizes a customer’s relation in the three aspects of attraction, expansion and maintenance.
A typical E-CRM strategy involves collecting customer information, transaction history and product information, click stream and contents information. It then analyzes the customer characteristics to give a transactional analysis consisting of the customer's profile and transactional history, and an activity analysis consisting of exploratory activities showing the customer's navigation, shopping cart, shopping pattern and more.
The benefits of E-CRM include the following:
- Improved customer relations, service and support
- Matching the customers' behavior with suitable offers
- Increased customer satisfaction and loyalty
- Greater efficiency and cost reduction
- Increased business revenue
Businesses that strategize and implement an E-CRM solution are able to align their processes around technology to effectively deliver seamless, high-quality customer experience across all channels. Customers have the power to help themselves through online personalized services that are made available on demand. The Internet provides a simple and ideal medium where customers can get information from websites, buy products and find answers using FAQ sections, forums or chat rooms.
8.8 E-SCM
What is E-Supply chain management (E-SCM)?
E-Supply chain management is practiced in manufacturing industries. E-SCM involves using internet to carry out value added activities so that the products produced by the manufacturer meets customers’ and result in good return on investment.
E-SCM is the effective utilisation of internet and business processes that help in delivering goods, services and information from the supplier to the consumer in an organised and efficient way.
Supply Chain Management flow
SCM flows can be divided into three main activities
1. Product Flow: The product flow includes the movement of goods from a supplier to a customer, and also any goods returned by customers.
2. Information flow: The information flow involves transmitting orders and updating the status of delivery.
3. Financial flow: The financial flow consists of credit terms, payment schedules, consignment and title ownership arrangements.
Advantages of e-supply chain management
Companies implementing E-SCM can enjoy the following advantages:
1. It improves efficiency
2. It reduces inventory
3. It reduces cost
4. It helps to take competitive advantage over competitors.
5. It increases ability to implement just-in-time delivery, increases on-time deliveries, which enhances customer satisfaction.
6. It reduces cycle time, increases revenue, by providing improved customer service.
7. It improves order fulfilment, order management, decision making, forecasting, demand planning, and warehouse/distribution activities.
8. It reduces paperwork, administrative overheads, inventory build-up, and the number of hands that handle goods on their way to the end-user i.e., the customer.
2. It reduces inventory
3. It reduces cost
4. It helps to take competitive advantage over competitors.
5. It increases ability to implement just-in-time delivery, increases on-time deliveries, which enhances customer satisfaction.
6. It reduces cycle time, increases revenue, by providing improved customer service.
7. It improves order fulfilment, order management, decision making, forecasting, demand planning, and warehouse/distribution activities.
8. It reduces paperwork, administrative overheads, inventory build-up, and the number of hands that handle goods on their way to the end-user i.e., the customer.
8.9 E-Security
Electronic security system refers to any electronic equipment that could perform security operations like surveillance, access control, alarming or an intrusion control to a facility or an area which uses a power from mains and also a power backup like battery etc. It also includes some of the operations such as electrical, mechanical gear. Determination of a type of security system is purely based on area to be protected and its threats.
Importance of Electronic Security System:
The electronic security systems are broadly utilized within corporate work places, commercial places, shopping centers and etc. These systems are also used in railway stations, public places and etc. The systems have profoundly welcomed, since it might be worked from a remote zone. And these systems are also utilized as access control systems, fire recognition and avoidance systems and attendance record systems. As we are know that the crime rates are increasing day by day so most of the people are usually not feeling comfort until they provide a sure for their security either it may be at office or home. So we should choose a better electronic system for securing purpose.
Classification of Electronic Security System:
Classification of security system can be done in different ways based on functioning and technology usage, conditions of necessity accordingly. Based on functioning categorizing electronic security system as follows:
- CCTV Surveillance Security System
- Fire Detection/Alarming System
- Access Control/Attendance System
CCTV Surveillance Systems:
It is the process of watching over a facility which is under suspicion or area to be secured; main part of the surveillance electronic security system consists of camera or CCTV cameras which forms as eyes to surveillance system. System consists of different kinds of equipment which helps in visualizing and saving of recorded surveillance data. The close-circuits IP cameras and CCTVS transfers image information to a remote access place. The main feature of this system is that, it can use any place where we watch the human being actions. Some of the CCTV surveillance systems are cameras, network equipments, IP cameras and monitors. In this system, we can detect the crime through the camera, the alarm rings after receiving the signal from the cameras which are connected CCTV system; to concern on the detection of interruption or suspicion occurrence on a protected area or capability, the complete operation is based on the CCTV surveillance system through internet. The figure below is representing the CCTV Surveillance Systems.
Fire Detection and Alarming Systems:
It can also referred as a detection and alarming system as it gives an alarming alert to concern on detection of interruption or suspicion happening on a protected area or facility. System generally consists of detector using a sensor followed by an alarm or an alerting circuit. The main function of this system is to rapidly extinguish an advancing fire and alarm tenants preceding impressive harm happens by filling the secured zone with a gas or concoction smothering operator. Different types of sensors are available for detection but usage of sensor is purely based on application requirement, like home automation, ware house fire detection, intrusion alert etc.
Attendance and Access Control Systems:
System which provides a secured access to a facility or another system to enter or control it can be called as an access control system. It can also act as attendance providing system which can play a dual role. According to user credentials and possessions access control system is classified, what a user uses for access makes system different, user can provide different types like pin credentials, biometrics or smart card. System can even use all possessions from user for a multiple access controls involved. Some of the attendance and access control systems are:
- Access Control System
- RF based access control and attendance system:
8.10 E-Banking
Electronic banking, Use of computers and telecommunications to enable banking transactions to be done by telephone or computer rather than through human interaction. Its features include electronic funds transfer for retail purchases, automatic teller machines (ATMs), and automatic payroll deposits and bill payments. Some banks offer home banking, whereby a person with a personal computer can make transactions, either via a direct connection or by accessing a Web site. Electronic banking has vastly reduced the physical transfer of paper money and coinage from one place to another or even from one person to another.
8.11 E-Trading
ETRADE is an online stock brokerage firm which offers investors the ability to buy and sell securities such as stock, future, options, mutual funds, bonds, forex and do online trading research without any interaction with a broker. ETRADE online platform comes with easy-to-use tools which enable users to maximize their trading experience; you can watch, trade, monitor stocks and view overall performance analytics.
How does ETRADE work?
To open an account with ETRADE you need a minimum of $500 to open a brokerage account. Just like most brokerage firm, you can fund your account by doing an electronic transfer from your bank or other financial institution, make a deposit into an ETRADE branch, or send a check via snail mail. Within a few days of making your initial deposit, you will be ready to start trading.
What Are the Benefits of ETRADE?
1.Beginner Friendly– Offers users an easy-to-navigate website with a great built-in education investor center. You can decide to do trading yourself or simply reach out to a broker. All this makes ETRADE an easy-to-use online trading platform for even the most novice of investors.
2.Manage Your Account– If you desire to take hands-off your investment, ETRADE has you covered through ETRADE capital management solution. This offers you a financial expert to help manage your portfolio. Their objective is to create and maintain a balanced portfolio that is persistent with your goals, risk, and tolerance. However, to take advantage of this option, you must have a minimum of $25,000.
3.Platform & Tools – ETRADE provides all traders with real-time streaming quote tool, Interactive charts, and even tax advice. However, the more active traders are automatically upgraded to the ETRADE Pro platform, which comes with extended trading hours, and additional tools like the ability to stream CNBC, customizable watch lists, and ETRADE 360 – which integrates all your investments into one place.
4.The length of Services– ETRADE can be regarded as a one-stop shop for financial services because it offers an extended spectrum of investments. This ranges from stocks and bonds to mutual funds and providing banking services to maintain checking accounts and IRAs, and can even apply for a mortgage.
5.Security– Everybody wants to sleep knowing their financial information is secure. ETRADE have a security-conscious reputation with ETRADE’s Symantec Virtual Digital Security Token, where you can receive a keychain-sized device that generates a 6-digit new personal access code every 60 seconds. There is also a Symantec app available for iPhone, Android, Blackberry, and Windows smartphones for individuals who have smartphones.
Pros & Cons
Pros:
- ETRADE’s website is easy to use and its research, investment, and a trading tool are ideal for beginners placing basic trades and experienced traders working on complex orders.
- Offers a reasonable minimum deposit of $500 requirement which opens the platform to investors of all sizes and levels of experience.
- You can operate as an investor using financial consultant assistance, or have your portfolio professionally managed.
Cons:
- More expensive trading fee than most online brokers.
- High commissions for infrequent traders.
- Active-trading oriented with perhaps only a few getting the benefits of lower fees.
8.12 E-Marketing
What Is E-Marketing?
Companies use e-marketing techniques, such as sending e-mail and advertising online, to market products to customers and increase traffic to their websites. Read on to find more about the skills and methods used in e-marketing.
Businesses use e-marketing, or Internet marketing, to reach consumers and market products to them. Methods for e-marketing often involve electronic communication and digital technology. To connect with consumers through e-marketing, a business may send e-mails to new and existing customers. They may also advertise on websites or alter content on their own sites to ensure that their businesses rate high in search engine results. Other advertising mediums, such as television and radio, can prove expensive, so e-marketing methods can be an attractive alternative to businesses that want to spend less money to reach potential clients on a global scale.
How e-Marketing Works
To increase traffic to one of its stores, a company may post a coupon on its website that offers customers an in-store discount. To entice customers to shop more online, a business may send consumers an e-mail offering free shipping for Internet purchases. Businesses also pay for advertisements on popular search engine sites. This way, even if a company's site doesn't show up in search engine results, it may be able to maintain visibility.
Here are different types of e-marketing strategies that can reach your consumers quickly and reliably.
1. Web marketing utilizes your company’s website to drive traffic with blogs, SEO content, and affiliate marketing. Your web page defines your business, products, and services.
2. Email marketing allows you to reach your entire consumer base at once with newsletters, promotional news, and more. This is the most widely used e-marketing strategy.
3. Viral marketing campaigns and video marketing are creative ways to share knowledge across platforms.
4. Omnichannel marketing solutions enable businesses to create sophisticated consumer journeys across email, mobile, social, website, print, and consumer care. Look for an omnichannel engagement solution to execute your marketing strategy.
2. Email marketing allows you to reach your entire consumer base at once with newsletters, promotional news, and more. This is the most widely used e-marketing strategy.
3. Viral marketing campaigns and video marketing are creative ways to share knowledge across platforms.
4. Omnichannel marketing solutions enable businesses to create sophisticated consumer journeys across email, mobile, social, website, print, and consumer care. Look for an omnichannel engagement solution to execute your marketing strategy.
Policy and Implementation:
Legal and ethical policy issues
Ethical Issues
In general, many ethical and global issues of Information Technology apply to e-business. So, what are the issues particularly related to e-commerce? Let’s list some of the ethical issues spawned with the growing field of e-commerce.
Web tracking
E-businesses draw information on how visitors use a site through log files. Analysis of log file means turning log data into application service or installing software that can pluck relevant information from files in-house. Companies track individual’s movement through tracking software and cookie analysis. Programs such as cookies raise a batch of privacy concerns. The tracking history is stored on your PC’s hard disk, and any time you revisit a website, the computer knows it. Many smart end users install programs such as Cookie cutters, Spam Butcher, etc which can provide users some control over the cookies.
The battle between computer end users and web trackers is always going on with a range of application programs. For example, software such as Privacy Guardian, My Privacy, etc can protect user’s online privacy by erasing browser’s cache, surfing history and cookies. To detect and remove spyware specially designed programs like Ad-Aware are present. A data miner application, SahAgent collects and combines Internet browsing history of users and sends it to servers. The battle goes on!
Privacy
Most Electronic Payment Systems knows the identity of the buyer. So it is necessary to protect the identity of a buyer who uses Electronic Payment System.
A privacy issue related to the employees of company is tracking. Monitoring systems are installed in many companies to monitor e-mail and other web activities in order to identify employees who extensively use business hours for non-business activities. The e-commerce activities performed by a buyer can be tracked by organizations. For example, reserving railway tickets for their personal journey purpose can be tracked. Many employees don’t want to be under the monitoring system even while at work.
As far as brokers and some of the company employees are concerned, E-Commerce puts them in danger zone and results in elimination from their jobs. The manner in which employees are treated may raise ethical issues, such as how to handle displacement and whether to offer retraining programs.
Disintermediation and Reintermediation
Intermediation is one of the most important and interesting e-commerce issue related to loss of jobs. The services provided by intermediaries are
(i) Matching and providing information.
(ii) Value added services such as consulting.
The first type of service (matching and providing information) can be fully automated, and this service is likely to be in e-marketplaces and portals that provide free services. The value added service requires expertise and this can only be partially automated. The phenomenon by which Intermediaries, who provide mainly matching and providing information services are eliminated is called Disintermediation.
The brokers who provide value added services or who manage electronic intermediation (also known as infomediation), are not only surviving but may actually prosper, this phenomenon is called Reintermediation.
The traditional sales channel will be negatively affected by disintermediation. The services required to support or complement e-commerce are provided by the web as new opportunities for reintermediation. The factors that should be considered here are the enormous number of participants, extensive information processing, delicate negotiations, etc. They need a computer mediator to be more predictable.
Legal Issues
Where are the headlines about consumers defrauding merchants? What about fraud e-commerce websites? Internet fraud and its sophistication have grown even faster than the Internet itself. There is a chance of a crime over the internet when buyers and sellers do not know each other and cannot even see each other. During the first few years of e-commerce, the public witnessed many frauds committed over the internet. Let’s discuss the legal issues specific to e-commerce.
Fraud on the Internet
E-commerce fraud popped out with the rapid increase in popularity of websites. It is a hot issue for both cyber and click-and-mortar merchants. The swindlers are active mainly in the area of stocks. The small investors are lured by the promise of false profits by the stock promoters. Auctions are also conductive to fraud, by both sellers and buyers. The availability of e-mails and pop up ads has paved the way for financial criminals to have access to many people. Other areas of potential fraud include phantom business opportunities and bogus investments.
Copyright
The copyright laws protect Intellectual property in its various forms, and cannot be used freely. It is very difficult to protect Intellectual property in E-Commerce. For example, if you buy software you have the right to use it and not the right to distribute it. The distribution rights are with the copyright holder. Also, copying contents from the website also violates copy right laws.
Domain Names
The competition over domain names is another legal issue. Internet addresses are known as domain names and they appear in levels. A top level name is qburst.com or microsoft.com. A second level name will be qburst.com/blog. Top level domain names are assigned by a central non-profit organization which also checks for conflicts or possible infringement of trademarks. Problems arise when several companies having similar names competing over the same domain name. The problem of domain names was alleviated somewhat in 2001 after several upper level names were added to com.
Another issue to look out for is Cybersquatting, which refers to the practice of registering domain names with the desire of selling it at higher prices.
Security features such as authentication, non-repudiation and escrow services can protect the sellers in e-commerce.
One needs to be careful while doing e-commerce activities. The need to educate the public about the ethical and legal issues related to e-commerce is highly important from a buyer as well as seller perspective.
Protection of privacy and Intellectual property
Protection of privacy
Government legislation and self-regulation are two major mechanisms for privacy protection. The effectiveness of privacy protection, however, depends on the joint effort of all the parties involved.
1. Government Legislation
The focus of government in privacy protection is to legally recognize subjects’ rights, to provide guidance and boundaries for collectors’ acceptable behavior, and to provide warnings and legal consequences for violators’ illegal and unethical behavior. In Europe, the European Community has taken aggressive legislative steps toward safeguarding privacy rights with respect to personal data processing.
2. Self-Regulation
We examine the privacy self-regulation initiatives along the categories of protection advisors, watchdogs, certification programs, and anonymity services. The examples provided in this discussion are used to illustrate concepts and are not meant to be a comprehensive listing of available products and services.
- Protection Advisors: People may not be aware how to protect their privacy. Various organizations, associations and centers focus on supplying privacy education for subjects. By providing various sources of detailed online privacy information, subjects can make informed decisions on how and when they disseminate personal data.
- Privacy Watchdogs: The focus of the privacy watchdog, such as EPIC (Electronic Privacy Information Center) and Alert (http://www.epic.org/alert/), is to identify violators and publicize their actions to alert privacy subjects. The CDT (Center of Democracy and Technology) unveiled a Privacy Watchdog site to help Internet users communicate their privacy concerns to Web sites and join an ongoing campaign to monitor the privacy practices of businesses operating online.
- Certification Programs: The focus of certification programs is to encourage the collectors to follow acceptable privacy principles, which will help to build trust among privacy subjects. Certification programs provide guidelines for privacy disclosures and associate a trusted and branded “seal” with sites that follow those guidelines
- Anonymity Services: While privacy is the ability of subjects to protect information, anonymity is the privacy of identity. Anonymity is essential to protect free speech. It can be used to protect activists of human rights, challengers of political policy, writers of controversial material, and others where revealing an individual's identity may threaten their life or wellbeing. However anonymity also opens the door for criminals to plan and coordinate attacks in an environment where authorities have no way to find and stop them.
Intellectual property
Intellectual property (well use the abbreviation "IP" from now on) is a legal term that refers to industrial property and to copyright and related rights. Industrial property comprises the protection of patents, trademarks, industrial designs, and geographical indications. It also includes the protection of utility models, trade dress and layout-designs or topographies of integrated circuits, where such protection exists, and protection against unfair competition including/or protection of undisclosed information/trade secrets. IP is really a type of property or asset, just as valuable (or more valuable) than physical or real property, even though it may be intangible, like knowledge. The value of IP assets relative to physical assets has increased because of the importance of technology and creative works in the modern economy. IP consists of new ideas, original expressions, distinctive names, and appearance that make products unique and valuable. IP is often traded (or licensed) in its own right without trading in the value of an underlying product or service, by means of patent or other IP licenses from a rights owner to another.
Finally, E-Commerce based businesses usually hold a great deal of their value in IP; so the valuation of your E-Commerce business will be affected by whether you have protected your IP. Many E-Commerce companies, like other technology companies, have patent portfolios and trademarksthat enhance the value of their business.
Next topic is coming soon
NOTE: for any queries please contact us
3. mail us aakashraj416@gmail.com






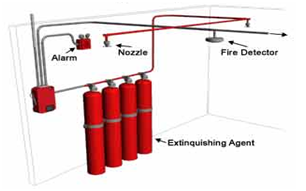







It's nice to read article about cxml, it will definitely help me in future.
ReplyDeleteCommerce XML?
Thanks for providing recent updates regarding the concern, I look forward to read more. pushpushgo
ReplyDeletethanks for the information nice blogs
ReplyDeletee commerce companies
thanks for providing recent information Ecommerce website builder |
ReplyDeleteMagento ecommerce development companies |
Great piece of information.
ReplyDeletedigital marketing companies in kochi
digital marketing company kochi
digital advertising agency in kochi
digital marketing companies in India
digital marketing company in India
digital marketing companies in kochi
seo companies in india
seo services in cochin
seo company in Ernakulam
best seo services in kochi
best seo company in india
Very informative post. Keep writing, all the best from Digital Marketing Company in Kochi - Hackney Solutions®
ReplyDeleteGreat post.
ReplyDeletehttps://www.question2answer.org/qa/user/AdliMajid
Great post.
ReplyDeletehttps://www.question2answer.org/qa/user/AdliMajid
Great post.
ReplyDeletehttps://forum.omz-software.com/user/johnanderson
Great post.
ReplyDeletehttp://www.cruzroja.es/creforumvolint_en/user/profile/111557.page
Great post.
ReplyDeletehttps://hubpages.com/@clintonmckelvey
Great post.
ReplyDeletehttps://wiseintro.co/virohaa
Good Post! Thank you so much for sharing this pretty post, it was so good to read and useful to improve my knowledge as updated one, keep blogging.thanks for your information really good and very nice
ReplyDeletehttps://speakerdeck.com/xfactor
Great post.
ReplyDeletehttps://www.debate.org/StephenTurk/
Thanks for sharing this blog. Retail sector is now facing is a shift from the offline to the online world. If you want to build Pharmacy App for your Pharmacy store then contact us today and go digital.
ReplyDeletetop-rated eCommerce and Amazon consulting agencyGood Post! Thanks very for giving this pretty post, it was so good to express and useful to better my information as renovated individual, hold site.gratitudes for your information honestly good and very agreeable
ReplyDelete"Thanks for sharing this. It’s exactly what I needed to read today!"
ReplyDeleteViral Mafia, the best digital marketing agency in Kochi.
ReplyDeleteGood Information. Best Packers and Movers in Kochi
ReplyDeleteNice breakdown of strategies. E-commerce omnichannel marketing automation really helps businesses stay consistent across channels
ReplyDeleteNice detailed notes on the fundamentals of online business models and digital transactions. The explanation of e-commerce types and frameworks also reflects the changing ecommerce vs retail landscape, where technology is reshaping how companies connect with customers and expand globally.
ReplyDelete